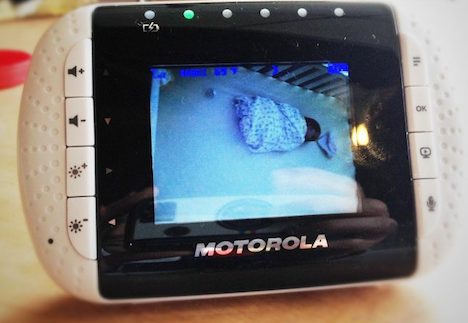
Baby Monitors, Security Cameras Among IoT Devices Too Easy To Hack, Say Israeli Researchers
By NoCamels Team March 13, 2018
This article was re-published with permission from NoCamels.com – Israeli Innovation News
Popular off-the-shelf IoT devices including baby monitors, home security cameras, and thermostats are easily breachable, according to an ongoing study by Ben-Gurion University of the Negev cyber researchers, who said they hacked into most of the devices in about 30 minutes.
The study, according to a university statement, is part of ongoing research into detecting vulnerabilities of devices and networks now found as part of “smart homes,” businesses and in the medical field. In January, BGU researchers warned that unpatched medical devices, such as computed tomography (CT) and magnetic resonance imaging (MRI) machines are too exposed to cyber threats and easily exploited.
The current research looked into 16 popular IoT devices from high-end and low-end manufacturers, according to the researchers at the Implementation Security and Side-Channel Attacks Lab at Cyber@BGU, the university’s cybersecurity research center. The findings were published in a paper titled “Opening Pandora’s Box: Effective Techniques for Reverse Engineering IoT Devices.”
In it, the researchers detailed serious security and design flaws they uncovered in the common devices by disassembling and reverse engineering them. Using “fault injection-based techniques (introducing faults to test code paths) for bypassing password protection,” the researchers were able to “recover device firmware and passwords,” and “discover several common design flaws which lead to previously unknown vulnerabilities.
Dr. Yossi Oren, a senior lecturer at BGU’s Department of Software and Information Systems Engineering and head of the Implementation Security and Side-Channel Attacks Lab at Cyber@BGU said, “It is truly frightening how easily a criminal, voyeur or pedophile can take over these devices.”
To continue reading this article on NoCamels.com, click here